Web3 Handwritten Report: Industry Hotspots and Explosive Products Not to Be Missed This Week
Original author: VIKTOR
Original translation: Peng SUN, Foresight News
GCR is an anonymous trader who rose to fame during the 2021 Bull Market for seemingly having a great grasp of market trends. As a well-known Short master with massive trading volume, his trading cases are impressive. For example, he openly shorted the top of DOGE in May 2021, shorted SHIB and Metaverse tokens in November 2021 (the peak of the Bull Market), and openly shorted LUNA before its collapse in 2022 (he made a $10 million bet with Do Kwon). Although he now speaks less frequently on social media compared to the last Bull Market, we can still read through his past tweets. This article has compiled some valuable insights worth saving and rereading.
Before reading the GCR tweets, I summarized and extracted some valuable points from the GCR perspectives worth learning:
-
The integer barrier is the Schelling point, which is either a potential support point or a resistance point, especially when there is no valuation reason.
-
Low unit deviation can attract retail investors: When you have millions of dogcoins (which are 10,000 times smaller than 1 USD), why would you buy less than a tenth of a bitcorne?
-
Do not short low Market Cap projects: if GCR follows this rule, you should do the same.
-
The strong always get stronger, and vice versa. Reducing the number of winning combinations and increasing the number of losing combinations is a bad strategy. It is better for you to go against the tide.
-
From the SNL and Musk's performance, Shorting every DOGE pump is one of the most successful trades you can take.
-
The advantage of GCR has nothing to do with K-line analysis or any complex strategy, it only relies on intuition.
-
Compared to the old Token, the new Token has one advantage: full of hope, lacking holders.
-
The market's reaction to news provides much more information about market participants' biases (bullish or bearish) and emotions than the veracity of the news itself.
-
Don't overthink it, just focus on making money.
-
During the altcoin cycle, you should maximize risk at the beginning and gradually reduce it over time, but most people do the opposite.
-
Asia/China will drive the next Bull Market.
-
BTC and ETH are both at the bottom. GCR turned bullish after the FTX crash.
-
Most people with long-term beliefs are better off holding BTC and ETH, rather than trading.
-
ETH will reach $10000.
Note: GCR was originally tweeted by @GiganticRebirth account, now using @GCRClassic, and there are also several tweets from the temporary account of GCR "MingXMecca".
Long-term, every time there is panic dumping due to Decentralized Finance vulnerabilities, because the market actually never cares about more than a few hours of time.
The market's reaction to news is very valuable for reference:
When news affects prices, market participants often struggle with whether it is true or false. More often than not, the actual truthfulness of the headline news is not important. The market's reaction to the news, and its reaction over a long period of time, is more meaningful.
**「Reverse Selling News」: **
When 95% of traders expect to 'sell the news' after the news is confirmed, I almost always buy, as I have said in the past, 'Reverse sell the news'. Many people who were forced to leave out of fear of a certain event are forced to rejoin. 'Selling the news' happens in unexpected circumstances.
Do not short low Market Cap projects:
That's why we never, never, Short low Market Cap projects. This is one of the hard rules I teach everyone, especially when sellers are exhausted after four years and supplies are in desperate straits.
Intuition is the greatest advantage:
The best traders will always put intuition first, not apophenia. Don't like this answer? Intuition is not enough to satisfy your curiosity? This is the truth, there is no other truth. I can't teach it to you, but you can find the edge.
Low unit bias effect can attract retail investor:
No matter how many times they see it, people still underestimate the attractiveness of the low unit bias effect on retail investors. This is the most powerful magnet in Cryptocurrency. Why would any sober-minded person buy 100 CONE, while retail investors would own 1,000,000? This is the cheapest Token on Coinbase.
Don't think too much except for making money
DOGE is the easiest coin to trade through the pump driven by catalysts:
Once you completely detach from these short positions, you will find that DOGE is the most easily tradable token. On April 20th, DOGE day, Musk appeared on the comedy show "Saturday Night Live" (SNL), and TSLA accepted DOGE payment. I shorted all the tops, and the enthusiasm for pumping can never meet expectations (a meme Token should not strive for fundamentals), and there may not be a cyclic low point.
Why profit from shorts?
The third most common question I receive is: If you still believe they will continue to decline in the long run, why profit on shorts? If you get a 70-90% drop space when shorting an AltCoin and still hold an extra 10%, please reassess your heuristic. If you're still mimicking my shorts discourse months later, this will happen to you.
shorts can be a type of trade or a type of contrarian investment:
There are two ways to shorts: trading and contrarian investing. If the confidence interval for the 1-year price is > 95% (there is a 95% chance that the price will be lower than the current one year later), it will "invest" and will not follow the short-term Fluctuation. I chose to "invest" in PEOPLE with 0.09 USDT; Squeezing into ATH is possible, but my investment is in a great company.
The Future of Non-fungible Tokens:
Comparing the Market Cap of Non-fungible Token projects with some famous meme Tokens: SHIBA reached a peak Market Cap of 60 billion; no Non-fungible Token has a cap of 1 billion USD (except BAYC). Relative to the rise of Non-fungible Tokens, AltCoin 2.0 seems to be overvalued; I predict that the tokenization of Non-fungible Tokens will erode the volume of AltCoin 2.0.
Hard integer throat is Sherrin point:
As expected, Rebound came out of 10 meme supports, but not entirely internet memes; hard integers are the obvious convergence point of fuzzy valuation of reflexive assets; Respect Xie Lin point.
Zone Rotation and Imitation:
For weeks I've been telling everyone that the biggest threat to any successful project is its own success. Success breeds imitation, and in this profit-driven industry, it will mercilessly shift to the original Derivatives to chase higher returns (from VC to traders to the final retail investor).
Decentralized Finance Summer, Food Farms, Original seigniorage [ESD, DSD], OHM (Olympus DAO), and countless other hot trends are rotating.
Short Elon Musk Stimulates DOGE Pump:
Has there been any trading strategy in the past year that is easier, more accurate (over 100%?), and less complicated than shorting Elon Musk to pump DOGE? A trade that requires less advantage, better predictive ability, and less talent, but always works? SNL, Dog Day, TSLA payments, Super Bowl ads, space missions, and so on.
Do not attempt to catch the bottom:
If I have helped you in the past, please listen to my advice: don't try to catch the bottom. You may incur huge losses, thinking that you can buy at a low price and recover some of the losses. This is almost impossible, and you are very likely to panic dump due to losses, or the currency price may go to zero.
Mastering Airdrop Chart Patterns:
Capturing (the) high volatility on both ends is where you can achieve the best returns, but the market has become increasingly efficient in pricing these events. However, Airdrops still often follow predictable chart patterns that the market has not fully mastered; study everything that has happened in the past 18 years.
Mastering the timing of Airdrop "bottom" is actually a very crucial art form that needs to be learned in this field; I really started studying this issue after UNI. Sometimes on-chain indicators are helpful, but this is in exchange; once the price flattens out and starts consolidating, sellers are usually exhausted.
Devote fully in interpersonal networking:
If you are not good at trading, you can try your best to build a network of contacts. Attend every meeting. Show up at every gathering. In a Bear Market, it is easier for humans to connect. You won't believe how many people I know who have succeeded by knowing the right people.
The famous 'Decentralization Casino' paper:
Just as 'digital gold' became the narrative and use case winner of BTC in the last cycle, the argument of 'Decentralization Casino' is becoming the Consensus of the entire encryption industry (filling the gap left by 'Web3').
For ordinary people, it's too expensive to fly to Macau or Las Vegas. When we have windfall gains and macro risks, Decentralization casinos and/or Decentralization Ponzi Schemes always run the fastest. I have always believed that humanity is desperate, greedy, corrupt, lonely, and trapped in the metaverse.
News Trading:
If you find yourself marginalized, I would suggest you trade the news instead of getting information from others. The competition for news trading is getting fiercer, so you must establish a fast-reacting infrastructure and observe projects that have been delayed for several months.
The most important thing is that if you are trading meme coins, when the market shows that they don't care about the 'news' of memes, you need to quickly cut your losing combination. Any traders who have an intuitive sense of the market can clearly feel this catalytic emotion and should take some profits at the first impulse.
The relative strength of stocks is often a lagging effect:
Traders often contact me asking why Crypto shows relative strength or weakness compared to stocks. I usually tell them to wait before drawing conclusions; most of the time, we are just witnessing a lagging effect.
GCR Short了一些coin:
Shorting SHIB, DOGE, GAL, SAND, MANA, original LUNA, LUNC publicly, and more generally, the Cryptocurrency bubble of the entire 2020-2021 and the macro-asset bubble lasting 10 years in the fourth quarter of 2021.
To be honest, due to some 'future catalysts', Token with Heavy Position of retail investors is often hyped for several months, leading to an explosive buying frenzy as the event approaches. Just when retail investors imagine that MEME will make them millionaires, market makers use the eventual Liquidity chain reaction for distribution.
Betting Unit Bias:
What caused XRP to rise to $3? The most important thing is the low unit deviation. BTC is already $10,000, ETH is $1,000. Retail investors feel that they are late to the game, but can XRP, which is priced at 10 cents, rise to $1? $10? How about $100? There is a lot of speculation that Coinbase will soon go public (which is not true) and betting on unit bias in the next cycle.
What really drives the development of retail investors in the AltCoin cycle? (1) I got into the 'legitimate asset class' (BTC/ETH) too late; (2) other coins seem to be institutional as well (XRP will be used by banks, Garling seems to be certified, ADA was created by the 'co-founder' of ETH, Musk endorses DOGE).
In the middle to late stages of the cycle, they start chasing the more decadent games that don't need so long societal proof (because the pool of retail investors has opened up). These cycles only start after the main assets have pumped for a long time, leading to (1) wealth effect; (2) people feeling they have missed the opportunity and chasing after altcoins.
For most people, it is too early to consider the next "institutional" coin. Doing research in a Bear Market will give you an advantage, but the real time to invest is after a significant pump in the major market. Emotions will also change from Cryptocurrency is an eyewash to "I need to buy the next ETH, ETH is too high".
Advantages of the new coin:
Full of hope; lacking holders; the team is not very rich, lacking motivation to speculate.
China and Asia will drive the next bull market:
I believe that China (and Asia as a whole) will provide the driving force for the next Bull Market, which will take quite some time to digest the Western ridicule of this space. However, the East is rising and eager to showcase itself. You should take a look on WeChat, where many future high-rises will be on Tokens that you are not aware of in your circle.
Strong Always Strong (MingXMecca):
In the narrative cycle, we have a cognitive bias towards buying Tokens that have not yet risen; but in the long run, the strong always get stronger, while the weak often continue to lag behind. Until the dance ends; then the created power quickly collapses.
"Low Float Theory" (MingXMecca):
Think about incentive measures, some projects have huge unpaid floating capital / in the future, hedging can be done. Let the market makers intentionally raise it, so that traders think they should join this 'narrative' - allocation; instead of selling at a price of 0 in a deep bear market later. They have been waiting for the echo of GCR.
Reverse Supercycle (MingXMecca):
Web3 has not seen any real change, people are just talking about their narratives at the top and bottom. I have always told people that the idea that all Tokens will go to zero is just the reverse of Supercycle, "this time it's different". It's always the same game, and people love Tokens.
The best-performing Token has the worst Tokenomics:
Some of the best-performing Tokens have the worst Tokenomics, coming from the most predatory teams. Many teams launched at the peak of the Bear Market have been desperately waiting for more favorable conditions so that they can deploy their tactics and manipulate the market.
Winner takes all, loser gets nothing:
Try to imagine your Ponzi Scheme as a professional boxer instead of a Token; winner takes all, loser gets nothing. People really do cut their winning combinations and increase their losing combinations instead of seeking treatment.
Increase risk at the beginning of the AltCoin cycle:
We observe the general trading principles when MEME coin rises: during the AltCoin cycle, you should increase risk when the trend reverses for the first time, and gradually protect capital over time. People lose money because their approach is exactly the opposite; slow in the early stages, and increasingly greedy over time.
I continue to hold a large position in Spot BTC and ETH because I believe we have bottomed out in November and remain optimistic about the future; aiming to achieve the target of $10,000 ETH by 2030. 90% of holders will be better off. This advice only applies to Degen traders playing with garbage coins.
The best indicator to know how much juice is left in an altcoin season:
Long has been trading in the altcoin season for a long time. One of the best indicators of remaining long juice is how AltCoins react to news, announcements, listings, and fraud. When the altcoin season is about to rug, traders are still going long on the news, but will immediately start dumping.
HODL Spot:
I bought about 16,000-18,000 Tokens in 2022, and I am not very interested in long trades. I plan to sell them to institutions/TradFi funds in the late stage of the next cycle. I have expanded the scale of some reverse investments and selected some narrative/rotation-exhausted selected junk coins.
Research 2019 and 2020:
Don't expect too much. The entire banking system will not collapse overnight, nor will it overnight lead to hyper-bitcoinization and push BTC to rise to $1 million. Don't expect too little either; when we get a correction, it's not CZ designed eyewash for exiting Liquidity, it's going back to zero. Stay balanced. Study 2019 and 2020.
ETH will reach $10,000 one day:
This may be my last tweet about Cryptocurrency. As I often say, if you have long-term faith in BTC and ETH, you just need to hold them without trading, and you will have a good return. They will only continue to print more long money; you are unlikely to catch every local move. ETH will reach $10,000 one day.

Disclaimer: Readers are strictly required to comply with local laws and regulations. The above content does not constitute any investment advice.
- Reward
- like
- Comment
- Share
August may become the major turning point for the encryption market
This is something I have been discussing openly for some time, but today I want to reconfirm that evidence suggests that there may be significant trends and emotional changes in the BTC and broader cryptocurrency market between August 6th and 12th.
A few months ago, I mentioned this time period for the first time in the video outlook, which you can find here.
Today, I will show all the evidence gradually established based on the time range, price range, and time perspective. I think you will see a high probability of significant events or news occurring within this time window.
We will start from the monthly chart and go all the way to the daily chart to show the convergence of multiple factors we see.
The monthly chart is the content we focused on following last week, but to further prove that we are in the same cycle, we have also included the months of the previous two tops. As you can see, the previous two cycles are almost identical to the current cycle. The 33 months from the major high point and the 20 months from the major low point both place us in the timeframe from July to September, which is the last low point before a significant pump.

Now we know that time is on our side, but many people believe that this cycle is different because prices have quickly reached new all-time highs. However, let's compare the current cycle with previous cycles on the monthly chart.
The evidence is quite shocking. As you can see, except for 2012, in the first two cycles, the price pumped just over 200% from the Bear Market low, which is exactly where we are now. As you can see, this time is no different. In fact, time and price are where they should be, neither overextended as some commentators have said, nor exceeding expectations.

Next, let's look at the weekly chart, and there is more long content to discuss. First of all, we found that there will be a major trend change every 30 weeks in this cycle. Interestingly, this 30-week cycle falls exactly between a major low and a major high, and they occur simultaneously. I will explain the reason in the next few charts, but for now, the next 30-week cycle falls exactly on the week of August 12th. These three 30-week cycles add up to a total of 90 weeks from the Bear Market low point.


Now, based on our evidence, this market is in a different stage, in my opinion, inflection point is more likely to occur in the form of a major low rather than a major high. But as I have always said, in these cycles, we often see a major high and low in this time window at the same time.
The chart below shows this particular period in each cycle and the situation at the same time last year in this cycle. As you can see, there is almost always a sharp pump in August, followed by a rapid decline, with a drop of up to 20-50%. Last year, it was different from the other three charts as it was only in the second year of the cycle, but it showed the seasonal characteristic of this type of trend occurring in August.

It also demonstrates that significant highs and lows occurred near the turning point of the market in a 30-week cycle, with a relatively tight time window.
Now let's take a look from a time perspective. Simply put, the time perspective refers to starting from a significant high or low point and calculating 30 calendar days, and looking for trend changes. You just need to start with 30, and then add 30, 60, 90, 120, 150, 180, and so on, and look for trend changes at these time points. The more concentrated the time points, the higher the importance of that day or week.
As shown in the chart below, all these time measurements fall within a time angle window. In this cycle, we have several major highs and lows that point to the second week of August as a major convergence period.

Finally, from the perspective of the time range, the market has always followed a cycle of 150 days in this cycle: 155 days of pump and 150 days of consolidation. It is worth noting that the balance of market time should not be imbalanced. That is to say, the number of days the market falls should not exceed the number of days of pump. In a Bull Market, the time of market pump is usually longer than the time of decline, as shown in the chart below. If the number of days the market falls exceeds the previous 150 days and new lows appear, this will not be a good sign.

Finally, taking into account the price range, time frame, timing, and seasonal factors, we are approaching a mid-August window that is very likely to become a trigger point for BTC. If this evidence is not sufficient, please note that the start date of the BTC chart is August 19th. I won't dwell too much on this issue, but the birth date is important, and August is typically the start of a major bull market.
This is why I remain cautious here and wait for the end of this window before taking more aggressive action. Will we see ETH ETF finally begin trading, followed by a rapid decline like BTC ETF? Or will we see more uncertainty caused by long political headlines leading up to the election? I'm not entirely sure what it will be, but it's definitely a period worth following and being patient with.
- Reward
- like
- 1
- Share
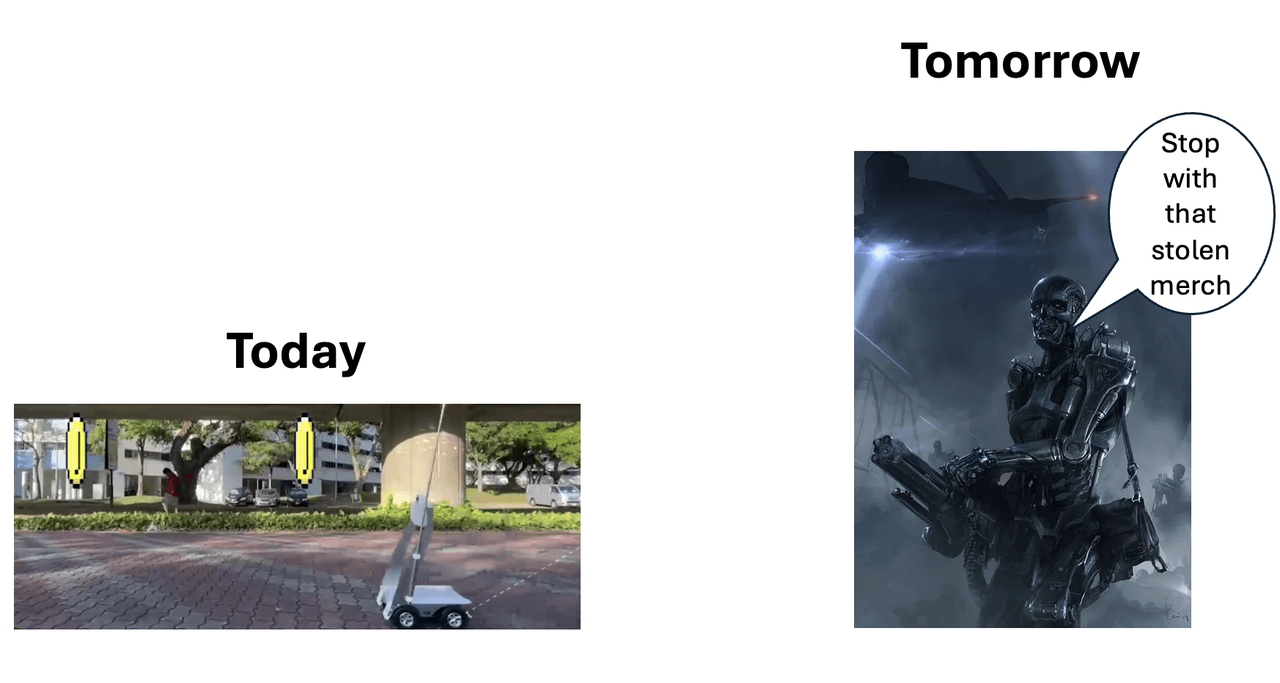
DeSec: Potential Applications of Decentralization Protocol in Monitoring and Law Enforcement
Original Title: "DeSec? Where Crypto Meets Security, Surveillance, and Defense"
Written by: Luffistotle, Zee Prime Capital
Compiled by Tia, Techub News
Lately, security order issues in the West have begun to emerge. Typically, we measure the quality of order by taking walks in cities and parks during the day and at night (to see if it is safe). But now this measurement is becoming increasingly unreliable. Social order is built and maintained through three components:
- Laws and Social Norms
- Law enforcement (police, surveillance, etc.)
- Judiciary (Application of Law)
The interaction among these three is complex and integrated with Depth. When people start to avoid walking in the park, or stores begin to move away from the original city for business (usually a very clear sign), it indicates that governance has problems. In fact, some current policies do have some problems. In fact, we can try to understand the possibility of crypto improving law enforcement, which will help improve social structure. Below we will discuss this, focusing on the application of crypto in monitoring tools.
Looking at the long river of history, during the period of declining trust in public institutions and protocol (law), society often resorts to vigilante justice to solve their problems. This power was originally meant to address real community issues, but it eventually turned corrupt and evolved into extortion.
Perhaps there are more modern solutions now, such as cheaper monitoring technology, which may provide 'leverage' for law enforcement agencies to solve problems in a scalable way to ensure the community's goals and desires are achieved. Technology can enable the same number of people to do longer tasks. And protocols of decentralization can help ensure that this new power is not used for other purposes.
The idea of strengthening law enforcement through surveillance is actually terrifying, because there is a threat of abuse of power.
"Absolute power corrupts absolutely."
Cryptocurrency brings the possibility of financial freedom—it eliminates the monopoly of the state on currency and balances the financial behavior of the state. Similarly, it can also balance new surveillance tools. By combining ubiquitous, inexpensive robots, cameras, and sensors with a reliable and neutral collaborative network, it can balance the state's surveillance monopoly.
In our category of projects called DeSec, we explore Depth through interesting conversations with experts. The security field is another opportunity for crypto because it is one of the few areas where clients (government, community) are willing to pay for insurance (defense is willing to pay for redundancy). Redundancy is an inherent feature of crypto. This feature is also why many encryption products usually cannot compete with other solutions, as crypto requires constant payment for higher levels of security/redundancy/verification.
That being said, redundancy is not necessarily a bad thing. It is a trade-off between deterministic fixed costs and variable future costs. In the case of BTC, its value and success are derived from the cost paid for achieving trustless validation (breaking Consensus requires a high cost, hence its security is high). In the defense manufacturing industry, the tolerance for security or failure rates is also extremely low, even if it requires a high cost to achieve.
DePIN meets DeSec: NeighborhoodWatchDAO
The majority of the value of DEP comes from shifting the burden of capital expenditure from companies/protocols to Node operators in exchange for a certain proportion of income. This provides the potential for expansion that many types of networks cannot achieve in other ways.
With these features, some instant applications can be introduced to the market. For example, Dempsey is a DePIN-style SoundThinking (formerly known as ShotSpotter) Node network, which can be sold to ShotSpotter itself or have its own protocol. For those unfamiliar, ShotSpotter is a microphone network installed on buildings that can triangulate the location of gunfire and alert law enforcement or emergency personnel for faster/immediate resource deployment.
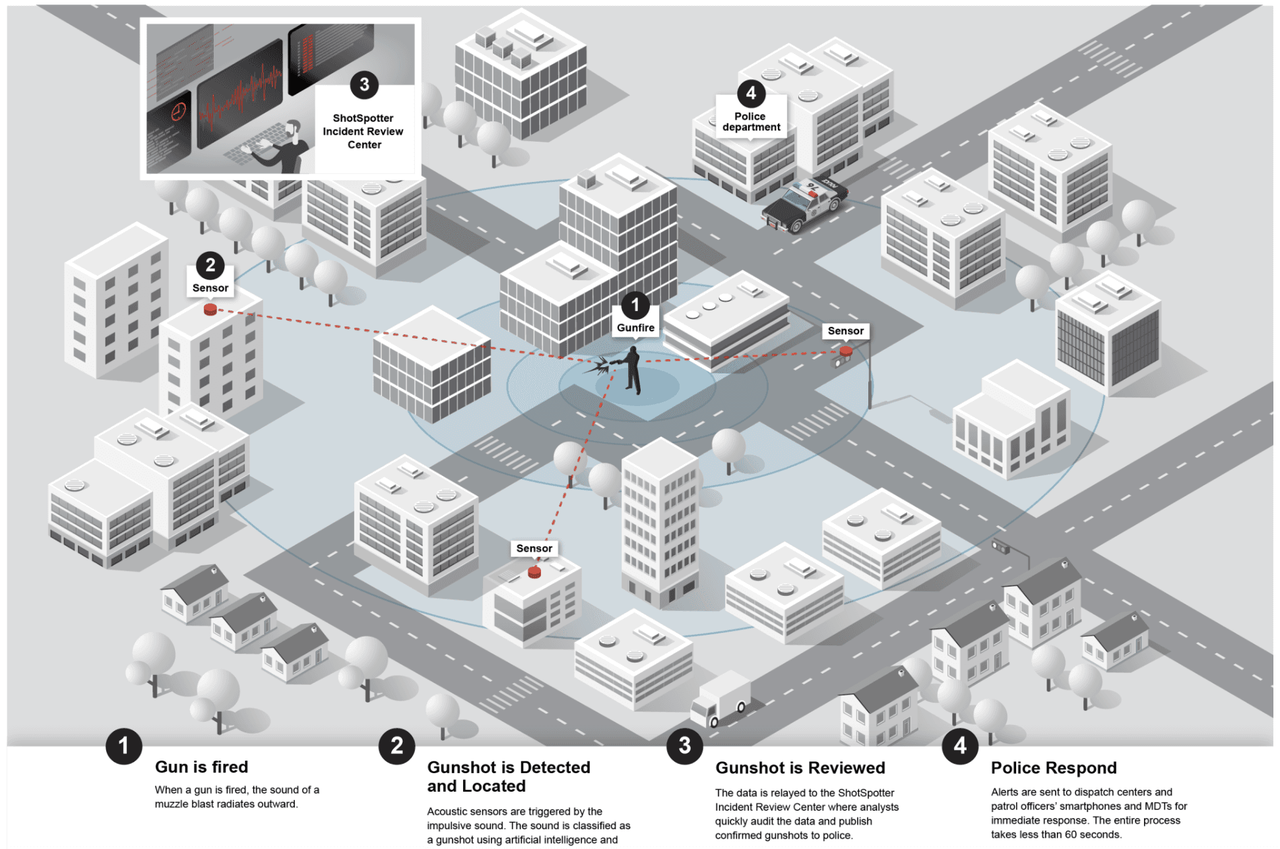
As Node operators deploy to their respective cities, such protocol can be extended globally, with a speed faster than the internal reinvestment cycle of companies like SoundThinking.
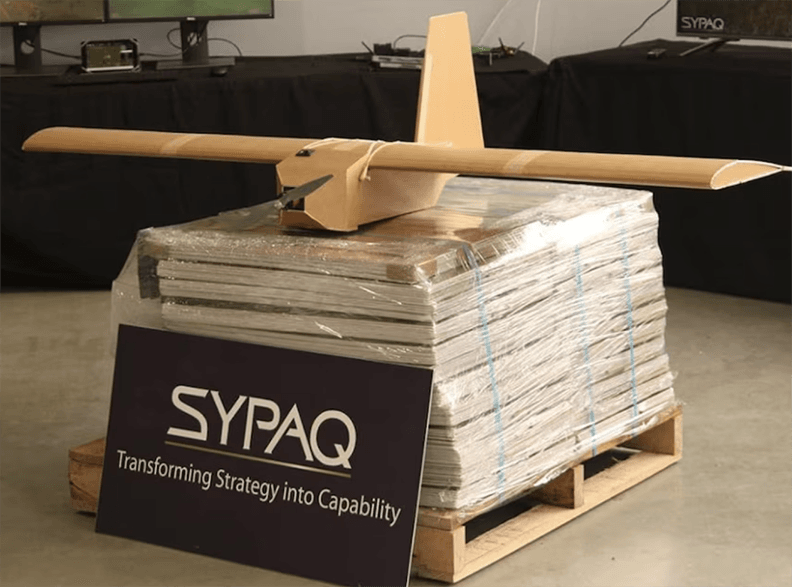
Similarly, the risk of small drones invading potentially important airspace is increasing. Just as the recent invasion incident at Langley bearish traders Base has shown us. While the US military may have classified solutions for such attacks, a different solution may be needed for other less secure airspace. Incentives can be provided for small radars or visual observation networks in relevant airspace to help law enforcement understand the situation at the launch point.
Similar models can also be used to observe signal strength. (Although this is usually provided by wireless providers to ensure network quality, wireless providers also have disadvantages, and their signals are usually transient.) DePIN can provide continuous signal quality monitoring for these networks (as some projects like ROAM have already planned to do). This is a simpler implementation solution.
In recent years, the number of cheap mobile signal jamming devices in the hands of thieves has increased dramatically. These devices are very frightening because you may find that when someone breaks into your house, your mobile phone, wifi, or radio cannot contact the police.

Criminals can place it in their waistbands and then rob your house or steal your car. Signal monitoring in cities and other areas can easily detect such interference events. Similar to ShotSpotter, it can also alert authorities.
We can also create similar protocols to incentivize regular patrols of small drones (Patrol2earn) in problematic areas, or we can leverage existing projects like DEPINS to support surveillance agencies. Projects like Frodobots or DIMO will use cameras to capture critical events.
Communication
Similar to the monitoring department, DePIN network can also be used to enhance the robustness of network transmission (whether it is an electrical network or a digital network). The advantage is that even in the event of a disaster, such networks can still remain stable.
The mesh edge network can resist today's highly centralized CDN-centric Internet traffic, while the Decentralization power plants can coordinate small-scale energy production, allowing these energy devices to provide backup power when the main production center becomes a target of attack.
This logic also applies to modern warfare. In fact, modern frontline forces need Decentralization more. As we have seen in Ukraine, the use of FPV drones is a significant development in the field of warfare. Small, low-cost (even cardboard drones) and fast precision strikes are now achievable. Any key facilities on the battlefield (i.e. logistics hubs, transmission/command shelters, etc.) will become targets for attack. This will result in these small facilities being called failure points, and the best way to deal with them is to use distributed communication.
In this economic situation, do you still want to use missiles?
Verification
Longer verification can be applied to robot manufacturing. Entering malicious instructions into manufacturing robots may pose serious risks to the entire manufacturing chain. One way to address this type of issue may be to perform Consensus-based verification of the code at runtime. This can help capture malicious alterations to the manufacturing process by reaching Consensus on the code to be executed.
Similar to validation, STAEX provides a public network to facilitate trustless communication between internet of things devices. This offers a novel way of communication for these devices and reduces the risk of interference through traditional channels. Given the increasing risk of illegal activities, this is an important technology that can build a strong network to enable these devices to transmit valuable data.
Other uses of verification include Palmer Luckey's citizen submission of evidence (snitch2earn) as mentioned above. Within the current legal framework, highly complex operations such as concealed identities and bait cars may be difficult to enforce, but nevertheless, in today's world, there are still plenty of ways to record criminal activities. A simple location can be set up to deploy data, and even contextually verify location/time through encryption (ZK!!!).
DeSci
DeSci is another way of integrating encryption technology with the defense/intelligence industry. For example, DeSci DAO funds research in previously overlooked fields such as materials science, bio-manufacturing (such as valleyDAO), cryogenics (CryoDAO), longevity (Vita), and human performance enhancement (does anyone want to join me in making a peptide DAO?). These DAOs can actually have a meaningful impact on these research areas. For example, HairDAO is now one of the largest non-balding research funders in the world.
I believe that as more and more long scientists are abandoning traditional research approaches, innovation in more long cutting-edge research will come from this type of DAO.
Why is protocol important
Why do we need protocols? Many of the ideas mentioned above are clearly aimed at enhancing the surveillance of national governance. However, assuming that these surveillance tools are brought to the market and managed by protocols. In this case, decentralized governance can check whether the authorities using them are enforcing the law properly, and whether the values of those monopolistic governors are consistent with the people they govern? If not, protocols can vote to decide not to provide value-added information to law enforcement agencies anymore (perhaps they will choose to support private police forces or private intelligence agencies).
Comments from skeptics

Increasing surveillance capabilities, regardless of who controls it, may have negative impacts on society. Do not overly question the practical possibility of Decentralization governance, because, similar to BTC, this protocol must rely on the principle of absolute non-permission, that is, minimal governance. That is, maximize the trustless nature.
Society is constantly evolving, and the ability to implement absolute rule of law may weaken our adaptability. Disobedience can promote progress, although it is a very specific form of disobedience (rather than street crime). How can we eliminate specific types of crime? If we make maximum use of monitoring technology, this may become a slippery slope.
Therefore, when implementing technology that helps maintain established order, we must be careful to protect privacy. We humans must have the ability to express outrageous ideas and resist tyranny. If the imbalance between law enforcement and resistance becomes too great, we are just promoting a minority-report style of tyranny.
If we delve deeper into this asymmetry, we can find that the right to bear arms in the United States has become meaningless. The goal of establishing the right to bear arms is to ensure the possibility of potential resistance, but once we invent missiles (not to mention nuclear weapons), this possibility no longer exists. Of course, the right of individuals to defend their property still exists, but it is ineffective in resisting the government.
Encryption technology has unique capabilities that can take the market to a new level. Will the future be MerceneryDAO, defense technology funded by encryption, community-owned drones, or liberal and pacifist? No one knows. Perhaps the answer lies in smaller parts, such as micro nuclear power plant monitors and drone protection networks of Decentralization, or perhaps in some places we haven't even considered.
- Reward
- like
- Comment
- Share
Layered Bitcoin: What are the main BTC L2 islands and how to integrate them?
zkLink's Mainnet 1.0 version will be launched within a month, and users will be able to trade Spot assets; in the next two to three months, users will also be able to trade Perpetual Futures using different on-chain funds; in the second half of Q4 or Q1 next year, there are plans to launch Non-fungible Token trading products.
Host: Frank, Foresight News Researcher
Keynote Speaker: Vince Yang, Co-founder of zkLink

"Founder's Dialogue" is a series of Foresight Talking AMAs launched by ForesightNews. The founders of various projects will share their entrepreneurial experiences, development experiences, industry knowledge reserves, financing processes, and future product market plans in the live channel. If you are interested in a project/founder, you can leave a message on our official Twitter (@Foresight_News) and @ the project's founder. We will select the most popular founders and invite them to our Twitter Space for intimate interaction with everyone.
In this issue, we invited Vince Yang, co-founder of zkLink, a multi-chain trading infrastructure. Not long ago, zkLink completed a $10 million financing. This time, we exchanged ideas with Vince Yang on how to use ZK technology to achieve a new solution to improve asset security.
**Frank: First, please let Vince introduce zkLink to everyone. When was it established, what is it currently working on, and what products have been launched?
Vince Yang: The product we are building is the first long-chain ZK Rollup protocol in the market, mainly using ZK technology to establish a unified trading infrastructure for the long-chain, aiming to improve various pain points of existing Decentralized trading products and build and support the next generation of Decentralized exchanges, including order book exchanges, Fungible Tokens and Non-fungible Tokens (NFTs), NFT trading markets, and more.
Frank: What role does Zero-Knowledge Proof technology play in zkLink's positioning as a "multi-chain transaction infrastructure based on Zero-Knowledge Proof"?
Vince Yang: The entire zkLink protocol adopts a classic ZK Rollup architecture, and we have made some innovations on top of the classic ZK Rollup architecture, with two aspects being the most important.
The first aspect is that we are not only connected to the Ethereum network, but also connected to long layer 1 blockchains and layer 2 networks, including Ethereum's Sidechains, such as the well-known BNB Chain, Avalanche, Polygon, etc., as well as the popular Ethereum scalability solution - ZK Rollup, a universal scalability network, including well-known zkSync, Starknet, Scroll, Linea, etc., as well as Polygon's ZK scalability solution, Polygon zkEVM.
At the same time, we are also integrating some non-EVM public chains, like Solana, in fact, we have completed more than 95% of the development work and Open Sourced the first ZK verification contract on Solana, but this verification contract has not yet been connected to our Testnet because it only supports a relatively simple Algorithm called Groth16, which is a relatively lightweight ZK verification Algorithm, and currently, Solana's mainnet Block chain does not support more complex ZK verification Algorithms.
The Algorithm we currently use is called the PlonK Algorithm, which belongs to the zk-SNARK category. In other words, the entire zkLink network and protocol are similar to the well-known ZK general scaling network on the market, but there are significant differences in architecture. This is because we connect a large number of layer one and layer two networks with many funding entry points, and send the state of the unified state machine to these different on-chain Blocks for synchronization and verification.
So we have longer funding access than other general scaling networks, and can directly interact with assets and liquidity in different Blockchains on-chain, different from other ecology. Users will find that on the protocol layer, they can directly trade assets from different ecology and use a Wallet to manage assets from different Blockchains. This is very different from the current decentralized trading experience, because most DEXs actually only have liquidity pools on one on-chain, even though DEXs like Uniswap and SushiSwap are deployed on many on-chains, they are not interconnected but independent on networks such as Ethereum and BNB Chain.
For example, even if they both have USDT, these two USDTs are actually different and cannot be combined when trading in different networks. At the same time, you need to use different Wallets to operate different networks, especially networks like EVN and non-EVM. For Solana, you must first download their own Wallet. In the future, the MOVE ecosystem may thrive and have its own trapAddress system and specific Wallet. For users, the more long blockchain they encounter, the more Wallets they need to download and manage, which is a pain point for user experience. But we want to improve this problem and allow users to trade and manage long-chain assets with one click, which will be a major improvement in user experience.
The first aspect is that zkLink will integrate a Smart Contract Wallet that supports user social account login, namely Account Abstraction (AA). This will provide users with a seamless trading experience, similar to the experience of using mobile numbers, emails, or social account logins for transactions on centralized platforms.
At the protocol layer, users can manage long different assets on various blockchains with a single account and Address, without managing the Private Key. This is because the underlying solutions for different Smart Contract wallets vary. If MPC technology is used, the user's Private Key can be managed through Sharding and social recovery rules can be set. In this case, the migration cost and learning cost for users are greatly reduced, and the entry barrier is also lowered.
Due to the adoption of ZK technology, the security of this product is completely consistent with on-chain products like Uniswap. Although ZK protocol creates an off-chain transaction execution environment, the shared security is still based on on-chain security. The validity of fund changes and transaction execution is ensured through Zero-Knowledge Proof, which means that all fund changes and transaction executions achieve finality on-chain and share the Consensus security of the mainchain.
If you are currently only connected to the ETH chain, it is as secure as the ETH chain itself. If you connect to a sidechain of the ETH chain, such as the BNB Chain, then it will be as secure as the BNB Chain.
The security of the long chain is somewhat different here, but to ensure security, we adopt a trustless design. In the off-chain transaction execution environment, there are roles such as Sequencer and Prover, which are similar to other scaling solutions. However, there is also a third-party network called a Witness outside the chain, such as market makers or Large Investors. They can read off-chain data from different block explorers and compare the Zero-Knowledge Proof and this state transmitted to the on-chain to see if they are consistent.
If consistent, it can ensure that long on-chain states are completely identical, and the information they receive is also the same, which completely eliminates the risk of collusion between off-chain actors, Sequencers, and the transmission of false information on-chain. Because on the ETH chain, you cannot directly read the deposit information on the BNB Chain, but in this way, you can ensure that the state root in the network is consistent with the unified state, ensuring that the risk of collusion is almost 0.
**Frank: Compared to other Decentralization trading protocols, how does zkLink achieve multi-chain trading of encryption assets, and how does the multi-chain architecture ensure security?
**Vince Yang:**We can achieve this, primarily because we use Zero-Knowledge Proof technology, this encryption cryptography can ensure security, and in the industry, Zero-Knowledge Proof technology is generally considered to be an irreversible proof technology that cannot be cracked by attackers.
Even the operator itself, such as the off-chain Sequencer, cannot deceive the on-chain verification contract. When uploading information from off-chain to on-chain, I need to generate a proof, which contains a prove key. These two keys are in one-to-one correspondence. If you successfully match them, then the information you declare is true, and the state transition, including changes in your funds, is also true.
Based on this premise, we introduce the long-chain architecture, such as deploying the Rollup verification contract on both the first-layer blockchain and the second-layer network of long, where it will simultaneously receive unified off-chain state tree and transaction information on these networks, including a verification of Zero-Knowledge Proof.
If all these contracts can complete this proof and pass the multi-chain consistency check, the entire verification process can be completed. As long as the results of off-chain execution and generation are returned to on-chain, the results are completely correct. This process ensures security, including the role of submitting off-chain data, which cannot submit false data or forge proof to deceive the on-chain verification contract and attack the contract.
In other words, as long as the verification is passed and the specifications are met, the submitted information is considered to be correct, ensuring the security of the verification process mathematically.
Frank: We all know that zkLink has just completed a $10 million financing round with investors such as Coinbase Ventures. So, where will zkLink allocate the funds? Besides financial support, what other assistance can these investment institutions provide to zkLink?
Vince Yang: Our main round of investment is mainly led by US funds, including one of the largest shareholders of ByteDance, SIG, which has invested in many Web2 projects. However, they have been involved in the Web3 field as early as a few years ago and have invested in many infrastructure and trading-related projects. In addition, there is a top trading team from Israel, 'Efficient Frontier,' and some small trading teams from the United States.
The funds raised in this round will mainly be used to support the rapid launch of the Mainnet, and to advance the development and launch of more long products, so that more long teams can adopt the protocol. At the same time, we are also considering launching incentive measures for the Mainnet at the appropriate time, which may include TGE, but there is currently no definite plan.
The biggest expense should be in the development itself, and possibly supporting some early adopters, especially in the early stages of development, the consumption of software and hardware is very large, requiring the use of cloud resources. The recent 'Dunkirk' test we are conducting is actually a very expensive test because we need to consume a large amount of cloud computing resources every day to generate products to help users recover funds.
Now because of the long number of people participating in this event, it is estimated that there are already 60,000 to 70,000 people participating in this event. Because zkLink has been integrated with 7 chains, each on-chain has dozens of different assets, and generating a Zero-Knowledge Proof is quite resource-intensive for each asset recovery.
To help all users recover all funds, a large amount of computing power is required. This test requires us to increase a lot of Computing Power, and also requires the purchase of a large amount of hardware, including GPUs, which are quite expensive. In the future, we may adopt some new hardware acceleration solutions, such as FPGA or AGIC chip-based acceleration solutions. We will follow the pace of market development and purchase these hardware acceleration solutions at the appropriate time to ensure that the Computing Power of our network is strong enough to support high-performance transactions.
As for the help our investors will bring us, it is obvious because our main investors are from North America, including Ascensive Assets, a fund from Europe, which is one of the largest Cryptocurrency funds in Europe.
Investors from different regions will help us establish a partnership network in the local area, introduce our products, protocol, and technical solutions to people around them; Secondly, they will also help local users to understand our protocol and the advantages of our products earlier; In addition, investors will also help us introduce upstream and downstream partners, such as Smart Contract Wallet, and some specific products built on our protocol, such as the Non-fungible Token trading market and DEX.
Although we know that the encryption community is globalized, there are still obvious regional characteristics in the entire development process. Therefore, projects from the Asia-Pacific region are more likely to quickly expand in the local relationship network. If we have local partners in different markets such as North America, Europe, the Middle East, and India, it will help us reach local communities and users earlier, allowing them to understand our products earlier. In addition, investors may also help us with user education, contact local media partners and exchange partners, etc.
**Frank: In the previous Twitter Space, we discussed zkLink's first user fund disaster escape test 'Dunkirk'. Vince, can you introduce 'Dunkirk' to everyone again? Who is it targeted at, what is its practical significance for the encryption industry, and what is the ultimate vision?
Vince Yang: "Dunkirk" is a very interesting test. It is the first project party in this industry to proactively exit and allow users to withdraw all funds stored in the protocol. Secondly, this is an interactive and interesting test. We originally planned to close the testnet on May 11th. From that time, users will be unable to use the applications on zkLink, and the team will remain silent.
Even under extreme conditions, such as the disappearance of the team or the closure of the protocol, funds previously stored in the contract can still be withdrawn. Through this test, we hope to let users personally experience that when their funds are stored in a protocol, they can still retrieve the funds even if the team disappears and the protocol is closed.
Recently, there have been some security incidents in the zkSync ecosystem, which may involve low-level code mistakes and malicious behavior. If a project has passed this test before going live, as long as it does not change the code, users do not need to worry about such situations. In addition, this 'Dunkirk' drill is based on the ZK technology features, which can also be done by other ZK project parties. By completing this test, they can ensure that the security of the protocol is one hundred percent ready, even if the network crashes or other events occur, users' funds can be fully recovered.
For users, we hope to let them know through this test that even in any emergency, users cannot predict when a catastrophic security event will occur, so when choosing projects and products, users should consciously look for those that can be 100% custodied and 100% fund-retrievable. Even those projects that seem very advanced and secure may not have been fully prepared in terms of engineering and practice. Only through inspection can they truly be considered 100% prepared.
Therefore, we hope that more long projects can be incorporated into the "Dunkirk" testing standard, even though there may be some minor differences in practical operation, the concept of "Dunkirk" should be understood and understood by more long people. As long as the entire industry works together to promote security testing and drills similar to "Dunkirk," the level of Decentralization of encryption products, especially transactional products, will increase, and these products related to user funds will become more secure. This will be a higher level of self-discipline and requirement. If everyone can adopt this standard together, the number of attack incidents will decrease, and it will be difficult to see very long bridges and Rug Pull projects, because they cannot pass this test.
**Frank: We also saw that zkLink opened the 'Dunkirk' test 24 hours ahead of the original plan. What was the consideration behind this?
Vince Yang: This is an interesting topic. Originally, we planned to shut down the network at noon today, but suddenly came up with the FTX event during the brainstorming.
When the FTX incident happened, they didn't notify anyone. The whole process developed very quickly, with no advance notice. Even at the last moment, many people believed they wouldn't go bankrupt. In the world of encryption, there are many surprises, and users cannot predict which platform will have problems in the future. Therefore, we hope to simulate accidents and disasters in real situations through this unexpected shutdown. We hope that this test will leave a deep impression on users and let everyone truly experience that in the world of encryption, no one will notify you in advance of what will happen. If something bad happens, it will definitely happen suddenly.
Therefore, we need to be prepared at all times, always follow Risk Management and fund security, and put them in a very high position. We conducted the 'Dunkirk' test 24 hours in advance, considering these factors.
Frank: Are there any other encryption projects willing to join the 'Dunkirk' plan? How will zkLink promote the communityization of 'Dunkirk' in the encryption industry?
Vince Yang: We do plan to turn the 'Dunkirk' test into a series, and we have received positive responses from some projects. Some Wallet projects are currently being planned and tested, and they are very supportive and enthusiastic about this idea and concept.
At the same time, we will also conduct longer 'Dunkirk' tests in the future, including major upgrades and the addition of important content. If I have major updates, such as adding other blockchains to the network, I may consider conducting new 'Dunkirk' tests again, so that everyone can feel safe even if some code has been changed, new features, assets, and products have been added.
We now have Spot trading, and in the future, there will be derivatives trading, especially for derivatives, as they themselves have many complex business logics, such as Close Position, close all positions, and liquidation operations. Therefore, in the event of a disaster, what are the rules for fund withdrawal calculation, and all of these need to be tested and verified, especially when it comes to complex financial logic, fund handling will become even more complicated. Therefore, we may introduce new tests and use them in other project communities.
Now, especially in those projects that are 100% self-hosted and 100% secure, there should be enough motivation to adopt the 'Dunkirk' test standards. Of course, these projects may need some technical adjustments because their product characteristics may be different, but what 'Dunkirk' emphasizes is a disastrous retreat, that is, whenever any event occurs, your funds are 100% safe and recoverable. I believe that in the near future, everyone can also expect to see the second 'Dunkirk' test.
**Frank: What are the follow-up plans and roadmaps for zkLink? What are the key directions that are currently being focused on, and is there anything that can be revealed about the next stage of development plans?
Vince Yang: Let me introduce our current situation. We have been running on the testnet for over 12 months. Our earliest product was a Curve on the long chain, for example, you can use USDT on the BNB Chain to purchase USDC on the ETH network. Currently, this product is still in the testing phase. The product we are launching is an exchange with order book functionality. It has been integrated with 7 chains, and spot trading has been tested for over 10 months, which is very stable and smooth.
In the next quarter, we will launch the Derivatives exchange feature, where users can use assets from 7 different chains as Margin to trade Open Positions under a unified account. For example, users can deposit assets such as ETH and UNI from the Ethereum network, or BNB and CAKE from the BNB Chain, into the zkLink protocol, and use assets from multiple chains as Margin for Derivatives trading. This feature is very friendly to traders and can greatly improve the efficiency of fund utilization.
At the same time, within the next 1-2 months, we will complete the integration of all ZK universal layer 2 network ecosystems. Currently, zkSync, Scroll, and Linea have been integrated, and we are developing and integrating Starknet, Polygon zkEVM. Each of these ecosystems has hundreds or more long-term projects with their own local assets. We hope to aggregate all assets in these ecosystems, so that they can be connected to the zkLink network. Each ecosystem will have a large amount of funds settling, and aggregating them into one place will make it the best trading platform for Liquidity on the entire network, because the most important thing for trading infrastructure is to provide high-performance trading and the best Liquidity.
When all major ecosystems are connected, users will be very willing to use the products here, because they can buy all the assets they want to buy in one place. We believe that for a considerable period of time, cross-chain bridges will still be a very complex, difficult to use, and not secure enough product.
Of course, the development of Cross-Chain Interaction technology is very rapid, and many new types of Cross-Chain Interaction technology have emerged, such as those based on ZK and LayerZero technologies. However, even if the Cross-Chain Interaction transaction itself is secure, the user experience is still not very friendly. This is because Cross-Chain Interaction transactions require having Gas Tokens on two different on-chain platforms, using different Wallets, and also require paying relatively high Cross-Chain Interaction Money Laundering fees. The entire process may also consume a lot of time, especially for active on-chain users. Managing multiple Wallets can be cumbersome, and if users need to frequently move funds between multiple chains, the cost will be very high.
Therefore, we hope to create a unified trading layer that aggregates assets from various ecosystems in one place, providing sufficient Liquidity, so that users can place a large amount of funds in this layer and buy and sell the assets they want in the DEX.
For users, they prefer to use a Wallet and store their funds in one place. We can also support users in gaining some profits, so that their idle funds can be utilized. In addition, for users who use high or heavy contracts, their multi-chain combined assets can be used as Margin to improve the efficiency of fund utilization.
Currently, we are actively following all of these major Layer 2 ecosystems, including the possibility of expanding to OP (Optimism and Arbitrum) and even MOVE ecosystems in the future, as long as these ecosystems are safe and thriving. At the same time of integration, we will also expand the applications that the trading layer can support, such as order book, Non-fungible Token exchange, complex structured financial products (Options), LaunchPad, Wallet, etc.
We expect that in about a month, the Mainnet 1.0 version of zkLink will be launched, allowing users to trade Spot assets on it; within two to three months, users will also be able to use derivatives to trade Perptual Futures with different on-chain funds; In the second half of Q4 or Q1 next year, we plan to launch NFT trading products, which is our rough plan.
- Reward
- like
- 2
- Share
After the launch of ETF, ETH experienced a short-term decline, but the approval of stake and UX upgrades will become long-term catalysts.
The globally distributed green energy network requires trusted accounting records of the production and usage data, followed by effective and real-time benefit distribution, efficiently incentivizing global participants to collaborate, utilize, and share.
Author: KK, Founder of Hash Global
Since the entry into force of the United Nations Framework Convention on Climate Change on March 21, 1994, governments, numerous non-governmental organizations, businesses, and individuals around the world have been making continuous efforts to achieve global carbon neutrality. We already have the production equipment and technology for green energy, and the usage scenarios for green energy have also been greatly expanded. However, a globally effective ecological network for green energy has not been effectively established, and I believe the core reason is the lack of globally credible data. The energy network also needs to be globalized and digitized.
A globally distributed green energy network requires a trustworthy accounting ledger to record the production and usage data, and then to effectively and in real-time allocate benefits based on this, thus efficiently incentivizing participants from around the world to co-build, co-use, and share the network. We need to record data in three aspects:
- Power generation and energy storage. When green energy is generated and supplied, data can be accurately and credibly recorded, with tampering or falsification costs exceeding economic feasibility, and can be transparent and traceable globally without permission.
- Trading. The transfer and trading of green energy;
- Consumption. Refers to the use of green energy;
To solve these data problems, we need:
- The physical layer's internet of things terminal achieves real-time data collection;
- The Network Layer can support secure and trusted data transmission and storage;
- Block chain is used as the Settlement layer. Data needs to be able to be trusted, verifiable, visible to the whole network, and support real-time Settlement;
We are excited to see that Arkreen is exactly such a global distributed renewable energy data network that integrates various technologies. Arkreen aims to connect global renewable energy devices (such as photovoltaic inverters, energy storage batteries, electric vehicle charging piles, etc.), ensuring the trustworthy transmission of physical world data to the digital world, realizing the value of trustworthy data by aggregating their connections; and further promoting the deployment and maximal utilization of more distributed renewable energy devices in a Decentralization Web3 manner, ultimately achieving the global zero-carbon goal.
Based on trusted data, Arkreen truly builds a data infrastructure for an energy network. Those who contribute to the energy network can receive fair distribution and incentives. Global contributors to the network can connect their photovoltaic power generation equipment or energy storage batteries to the Arkreen network, and Arkreen will provide network incentives based on the data from these green energy devices. The green energy data on the network can lead to the development of applications such as green power certificates and virtual power plants. The authenticity of the data, or a trustworthy ledger, is the core of the entire network!
In the past, due to the highly fragmented and long-tail nature of the green energy market, the traditional top-down internet of things platform construction model could not connect a sufficient number of green energy devices within a foreseeable time frame. Without a sufficient number of device connections, it is impossible to support the commercial operation of mature energy network applications, thus falling into a 'chicken-and-egg dilemma'.
We believe that the Arkreen team can effectively break the deadlock and achieve the network's cold start and ecological flywheel effect in a short period of time using the incentive model of Web3. We will see the power of a permissionless network in incentivizing long-tail participants. The combination of the internet of things and blockchain technology gives us the opportunity to use the power of the community to build an energy data infrastructure network from the bottom up. We believe that Arkreen has the opportunity to become a model project in the direction of Decentralized Physical Infrastructure Networks (DePIN) in the field of Decentralization energy.
Imagine a scenario where John, who lives in Silicon Valley, California, installs rooftop solar panels, energy storage batteries, charging stations, and smart thermostats at home. These devices are connected to the Arkreen network through digital technology, and the data from the energy devices is collected and stored on the on-chain Block. One day, the California government calls on residents to reduce electricity usage for the next two days to relieve the power grid's voltage pressure, and the power company can provide incentives to residents who are willing to cooperate. Based on John's electricity usage habits, Arkreen can pre-charge the energy storage batteries and lower the temperature in his home, and then reverse output power to the grid for the next two days. As a result of this grid dispatch, John receives a reward from the power company. John can also open the Arkreen app and, based on the on-chain data of 900 kWh of solar power generation at home, claim 0.9 Renewable Energy Certificate (REC). These 0.9 REC, along with REC from other users in California, can be bundled and sold to a BTC mining company in South America for the purpose of offsetting the carbon emissions from BTC mining power consumption.
All of these will be the economic value that the Arkreen network can introduce from the real physical world. The generation, purchase, and circulation of green certificates in the Arkreen network are just one use case of the Arkreen network. Once the data is trustworthy, we will see more long applications emerging. Once the energy network is truly digitized based on blockchain, assets such as green certificates and carbon certificates can not only be flexibly divided but also have no geographical restrictions. They can also play a network effect and efficiently connect with various decentralized finance decentralized financial ecosystems. The history of users' purchase of green certificates and carbon certificates can also be presented in the form of non-fungible tokens in their on-chain identity.
With the vigorous development of various Web3 applications, the number of users with on-chainWallet or identity will become longer and longer, and the threshold for use will be lower and lower until they are completely insensitive. After opening the Arkreen APP, users (institutions or individuals) can easily purchase any number of green certificates at any time with a certain currency stablecoin or ETH in their wallet to offset their carbon footprint. The green certificates held and destroyed by users are visible across the network, thus becoming part of their reputation in the digital world. You can imagine that under the existing energy data network and green certificate certification process, the process of using Web2 Internet to purchase a green certificate will be cumbersome, and it will be even more difficult to prove "carbon neutrality" by yourself. If demand cannot be stimulated, supply will not be able to rise effectively, and the goal of global carbon neutrality will not be achieved.
The Arkreen team members come from industries such as internet of things, digital security, and blockchain, and have successful global cases in business models, product design, engineering implementation, etc.
- Reward
- 2
- Comment
- Share
BlackRock: ETH ETF is a complement to BTC ETF rather than a substitute
The myth of getting rich quick with MEME and BRC20 in this round has caused many friends to regret and reflect on where they went wrong, making them feel frustrated.
Many people say it's because of prejudice, they look down on things like meme tokens, only like to play some valuable support of the serious projects, resulting in missed opportunities.
Speaking of not being interested in prejudice, I basically don't pay attention. Even if others are bullish, I don't take it seriously. Why? There is a very important reason, there are still many things of my own that have not been completed. Before doing what needs to be done, I will cherish my attention very much.
Moreover, seizing opportunities is not a simple task. Rather than relying on luck, I believe in being prepared. As long as the preparation is sufficient, luck becomes almost inevitable.

So is it prejudice to say that this opportunity cannot be seized? I don't think so. If it is purely caused by prejudice, it means that the person involved does have strong comprehensive ability, and can seize the opportunity with just a thought. It's like being a complete Versailles, isn't it?
Can we take a look at those stories of getting rich overnight? Is their entire money-making logic achievable as long as you have no bias?
No, it's not.
For example, timely information channels, first-hand operation at the first time, timely cashing out and holding, chase the market, chase competitors, this series of operations involves complex factors and cannot be replicated.
And a person's review process is easy to be subjective, and many decisive details are ignored, such as luck factor, coupled with media rendering, we often only follow the results, resulting in the illusion that if I had done that at that time, I would have been fine.
If I don't talk about the harm of prejudice, I can actually find a lot of rationality in prejudice for everyone.
First of all, it is understandable to have feelings of regret. The opportunities in the crypto world are so long that we cannot catch them all. It is very normal to miss big opportunities. It can be said that if you want to regret, the crypto world will give you the capital to regret every day.
Then prejudice I can also understand, everyone has their own way of making money and values, sometimes prejudice can be beneficial.
Prejudice can focus on familiar things and block out things you don't understand, thereby reinforcing your preferred way of making money.
There are four issues in trading that need to be addressed. If any one of them has a loophole, it will definitely be exploited by the market, and being hit is only a matter of time.
1. Confirm the trend (judgment of long or short)
2, find the get on board location
3、Set take profitstop loss
4. Fund Management
Today we talk about the last one, fund management. If we compare it to a car, controlling the weight of the position is like controlling the speed of the car. When driving on a flat road, it is natural to drive faster and the risk is lower; when driving on a bumpy road, if the speed is too fast, it is easy to cause traffic accidents.
So, how to reasonably control the Position is a highly technical activity. Quantitative Hedging is like the steering wheel of a car. If used well, it can smooth the fund curve and also reduce the drawdown of funds.
Take profit and stop loss are like the brake system of a car: when encountering danger, immediately hit the brake, that is, close all positions, which is stop loss;
The road is too good, the car is too fast, it is easy to be dangerous, so you need to slow down, that is, gradually Close Position, this is take profit. Therefore, to drive a car well, you must skillfully control the steering wheel, speedometer, brakes, and accelerator.
Position in general fund products is usually around 30%.
Positions below 20% are referred to as 'extremely safe positions'.
20%~40% of the Position is called "moderate safety Position";
More than 40% of the Position is called "high risk Position".
This is equivalent to the speed of a car. 20% of the Position is equivalent to a speed within 40 miles per hour, and 40% of the Position is equivalent to a speed of 100 miles per hour.

If the road is safe, the car can drive at a speed of over 100 miles per hour; if in urban areas or mountain roads, it is best to reduce the speed to 40 miles per hour or even 20 miles per hour.
In a wave of market fluctuations, there are usually three methods to increase the position:
Pyramid increase the position strategy, inverted pyramid increase the position strategy, and uniform increase the position strategy.
1. Pyramid Buying Method
The Position is the largest when Build a Position for the first time, and the quantity of each increase the position is less than the previous one (the reduction quantity varies from person to person).
2. Pyramid Accumulation Method
The first time Position is built, the Position is the smallest, and each subsequent increase in the position is larger than the previous long (the increase amount varies from person to person).
3, Uniform Incremental Positioning Method
The quantity of the first Build a Position and each subsequent increase the position is the same.
There is also a rhombus Position method, which divides each round of the market into three Build a Position, with the first and last Position being small, and the middle one being larger;
The initial Position for the account is: 3%, 5%, 3%;
When the account is profitable by 5-15%, increase the Position, and the opening rate each time is: 5%, 8%, 5%;
When the account profit is 15-25%, continue to increase the Position. The opening rate each time is: 10%, 15%, 10%; When the account profit is 25-45%, start reducing the Position. The opening rate each time becomes: 10%, 10%, 5%; When the account profit is above 60%, continue to drop the Position. The opening rate each time is: 5%, 10%, 5%;
If the account starts with a loss, reduce the opening rate to: 2%, 3%, 2%; or even Build a Position only 2 times, each time at 2%; 01928374656574839201
What is the essence of this diamond-shaped position-adding method?
-
Increase fault tolerance with lower initial position. Most people experience large drawdowns due to excessively large or aggressive positions.
-
When making a mistake, drop the position size to avoid being affected by unfavorable conditions and emotions, ensuring survival and longevity.
-
After making the right moves, with profits and a safety cushion, you can be appropriately aggressive and expand your gains faster;
-
After achieving good results, start to be subtle, drop risk and drop drawdown; of course, individual investors do not need to completely copy this operation method, but to learn the excellent concept behind this method and decide according to their own willingness to take risks based on their own financial situation!
Today's article ends here. If you think it's well written, you can give it a follow and keep an eye on it~
Welcome everyone to join the discussion group and communicate together!
The article ends here. I will provide more detailed analysis in the communication group. If you want to join my circle, please contact me directly via WeChat below!
Join us:
VIP Group: People who agree with the values of this community, are willing to learn and develop independent thinking skills, and share the same goals. The purpose of the group is to focus on knowledge sharing, cultivate independent thinking, and allow everyone to learn and accumulate in the Bear Market, and achieve financial freedom in the Bull Market. Only when you transform this knowledge and skills into your own, will you have the ability to think independently and escape the fate of being a sucker. Welcome to join the VIP Group! ↓******

- Reward
- like
- Comment
- Share
Why did 'chain abstraction' become a popular narrative after 'modularization'?
With the development of technology, more and more people realize the impact of MEV on a larger industry and propose longer response strategies. The 'Arbitrage opportunities' of MEV may gradually decrease.
Author: Ebunker, WebX Lab
Blockchain technology enables people from all over the world to have the freedom to transact, bringing a brand new economic model to the forefront. P2P payments that resist censorship, Decentralized Exchange, permissionless lending protocol, and a series of innovations have created a fair opportunity for everyone.
However, the scene behind the encryption network activities is more complex—players with asymmetric information advantages are using various channels and technologies to exploit or steal opportunities from ordinary users, the most notable being through MEV (maximal extractable value).
MEV Introduction
MEV is used to describe the behavior of reordering transactions to obtain the maximum extraction benefit when generating a new Block (which will be added to a certain blockchain) for as long profit as possible. It can also be understood as the extra value squeezed out of a Block beyond standard rewards and gas fees by selecting which transactions to add in what order.
MEV is often associated with the Ethereum network because Ethereum has a highly important Decentralized Finance ecosystem. The more complex transactions involved in a Block (such as Smart Contracts related to lending or trading), the longer the opportunity for Block producers to earn additional profits by deciding to add, remove, or reorder certain transactions.

The basic principle of MEV
Block producers (commonly known as 'Miners') play a crucial role in protecting and maintaining the blockchain network. They are responsible for validating transactions and adding them to the network in the form of blocks. Which transactions are added to a block depends on the block producers. In a truly fair economy, transactions should be processed in the order they are received.
However, the incentive mechanism of the Block chain means that Block producers will choose transactions based on their profitability. This means that transactions with high Money Laundering will be prioritized, which is why users pay higher gas fees during busy periods. If Block producers choose transactions with higher Money Laundering, they will make more profit. Therefore, transactions with lower Money Laundering need to wait longer to be added to the Block.
Miners are responsible for packaging user transactions into Blocks and can also determine the order of transactions. This allows them to potentially gain additional profits from the market by reordering transactions, inserting their own transactions, or other means of manipulating the latency in certain situations.
For example, suppose someone initiates a large transaction with Decentralization Exchange (DEX), which may cause the price of a certain Token in the exchange to change.** A Miner can insert their own transaction before this large transaction, buy the Token that is about to pump in advance, and then sell the Token immediately after the large transaction is completed to make a profit. This phenomenon is similar to being sandwiched between two slices of bread, and is therefore called a "sandwich attack".**
MEV may lead to some issues, including increased competition among Miners, rise of Money Laundering, and drop in the security of the Blockchain network. To address these issues, researchers and developers are looking for ways to mitigate the impact of MEV, such as improving the Consensus Algorithm or designing more secure and transparent applications for Decentralized Finance (DeFi).
Forms of MEV
Of course, MEV is not equivalent to a 'sandwich' attack; the 'sandwich' attack is just one form of MEV. Currently, MEV mainly takes the form of front running, arbitrage trading, loan liquidation, and other forms.
front running
MEV searchers and Block producers can leverage their ability to sort transactions in the Block. For example, front running an important buy order that is still waiting to be executed in the transaction pool, or participating in the Allowlist of certain Non-fungible Tokens ahead of others. By inserting a similar buy order before the transaction, they can capture MEV when getting a more favorable price before the large buy order is executed.
Arbitrage Trading
When the price of an asset is inconsistent across different trading platforms, there will be an Arbitrage opportunity. In the Cryptocurrency field, the pricing of the same Token on two different DEXs may vary. Arbitrageurs use pricing differences to trade and profit from them. When a searcher's bot identifies pending transactions and inserts its own transaction before them to extract the value provided by the Arbitrage opportunity, MEV is generated.
Liquidation Trading
Decentralized Finance allows users to borrow against their deposited digital assets as Collateral. If there is a Fluctuation in the market and the value of the Collateral falls below a certain price, the position will be forcibly Closed. The involved Smart Contracts typically provide rewards or fees to the transaction that triggers the forced Close Position. When any searcher or Block producer running the robot discovers such a transaction, they can insert their own forced Close Position transaction into the Block ahead of others to receive the reward.
There are two places to get MEV in the liquidation of a forced Close Position.
The first scenario is to become a liquidator. Take AAVE as an example. User A deposits 5 ETH at a price of $4000 and obtains a $10000 USDT loan. When the price of ETH drops to below $2100, their position will be automatically liquidated to repay the borrower. Liquidation bots can monitor these events and intervene at the exact liquidation moment to carry out the liquidation and charge the corresponding fees.
The second scenario is when the borrower violates the protocol and must pay the liquidation premium. In addition to the service fees, the liquidation bot will also charge additional fees from the borrower.
Types of MEV
From a typological perspective, MEV can be divided into the following categories:
Sovereign MEV
The Blockchain Community can try to control its own MEV through sovereign MEV, that is, by setting the protocol rules for extracting MEV, allowing or disallowing certain strategies for extracting MEV, and specifying which links may obtain MEV revenue. The protocol community can use sovereign MEV to determine priorities and the way MEV is generated. For example, for some blockchains with sovereign MEV rules, violating validators may face corresponding penalties.01928374656574839201
Internal MEV
Internal MEV refers to on-chain generated MEV that is specific to the application block. This form of MEV allows application developers to set rules for capturing MEV in a reasonable manner. For example, an arbitrage trading strategy can be used to set buy orders on one trading platform and sell orders of equal quantity on another trading platform.
CeFi-Decentralized Finance MEV
Using the price differences between Centralized Exchange platforms and Decentralized Finance applications to conduct Arbitrage. The asset prices on Centralized Exchange tend to be updated before repositioning on-chain trading pools and DEX Liquidity providers. Due to the frequent activities of Arbitrage traders, CeFi-Decentralized Finance MEV is one of the major sources of MEV.
Cross-Chain Interaction MEV
Taking advantage of the fact that most blocks on the blockchain operate in isolation, they are not allowed to see what happens on other blocks on-chain. For example, the BTC network cannot see transactions on the ETH blockchain without using a third-party Oracle Machine.
Cross-Chain Interaction MEV allows traders to profit from Cross-Chain Interaction asset swap by analyzing data from different blockchains through Cross-Chain Interaction bridges or DEX. Cross-Chain Interaction-related Arbitrage strategies typically occur in blockchains like Cosmos.
Pros and Cons of MEV
The pros and cons of MEV depend on whose perspective is taken to view this issue. Objectively speaking, MEV is beneficial for the long-term security and price accuracy of the blockchain, but it is detrimental to end users.
On the one hand, MEV incentivizes economic coherence. By constantly monitoring prices, Arbitrage robots tighten the price spread and minimize discrepancies, ultimately providing more accurate and consistent prices. Additionally, higher network fees provide increased security guarantees. Given the potential for greater profit, more long robots participate in the computation process, thereby making the network more decentralized. This also further encourages Block producers to stay online for Mining or validating Nodes to increase participation and enhance network security.
On the other hand, MEV is not friendly to the vast majority of end users. The various Arbitrage operations mentioned above will tilt the balance of potential user groups towards the 'scientists (referring to professional users who can use programs)', crushing the vast majority of ordinary users in terms of funds and technical knowledge, and capturing value from them.
Development Trends of MEV and Various Countermeasures
Ethereum's founder Vitalik Buterin admits that MEV will always exist in Ethereum. validators can always prioritize transactions with higher fees, even if these transactions clearly come from 'front running' or 'sandwich attacks'. MEV traders will try their best to maximize profits using Arbitrage and other technological variations.
From an optimistic perspective, MEV can also be intervened. For example, developers can add relevant rules for sovereign MEV mentioned above to determine who can receive rewards and how to extract MEV from the blockchain.
**Ebunker partner 0xTodd stated that from a technical perspective, because Ethereum is a distributed network, it is never possible to determine what is absolutely fair 'first come, first served.' Therefore, it is technically impossible to 'eradicate malicious MEV.' However, ETH can mitigate the exploitation of MEV for certain users from a mechanism perspective, such as the proposed role separation between block producers and packagers to be implemented in the Ethereum Beacon Chain update. The introduction of long roles will significantly increase the privacy of user transactions and reduce the impact of sandwich attacks on users.
Here are some strategies in the market for MEV Arbitrage:
Developer Codeforcer proposed a method to combat sandwich attacks using the Salmonella and Uniswap pool's Smart Contract. The Smart Contract uses a 'Poisoned' Token, which will deplete the attacker's assets used for attack if they target Smart Contract transactions. CodeForcer has used this strategy to deplete 100 long ETH tokens from attackers (but currently, the Arbitrage bots in the market have upgraded and adapted to this strategy).
According to an organization called 'MEV Blocker', validators using 'front running' have obtained a value of up to $1.3 billion from DEX users. MEV Blocker users can add RPC endpoints to their ETH Wallet to avoid 'front running' and 'sandwich attacks'.
**FlashBots' 'MEV Protection' is another attempt to solve the problem of front-running bots. As the largest MEV protocol on the ETH network, it also provides free privacy RPC services, allowing users to submit transactions directly to validators, making their transactions invisible in the MEMPOOL. In theory, if the transaction is invisible, the bots cannot execute 'front running' or 'sandwich attacks'.
The non-custodial Wallet Blockwallet also integrates a feature called 'FlashBots Protection'.
Ethereum Research proposed a method called MEV Smoothing, which will make the MEV income of validators more consistent. This method indicates that the committee can confirm new transaction blocks and distribute rewards evenly.
In addition, Chainlink's Fair Sequencing Service (FSS) has also proposed a solution to the MEV problem. First, FSS aggregates transactions into Blocks and arranges them in chronological order. Then, it encrypts the data on-chain to protect it from being prematurely exposed to Miners or Block producers (until the transactions are packaged). According to section 5 of Chainlink 2.0, FSS attempts to ensure the fairness of this activity by using Smart Contracts (rather than individual Nodes) with this capability.
In the long run, with the development of technology, more and more people realize the impact of MEV on a larger industry and propose longer-term response strategies, and the 'Arbitrage opportunities' of MEV may gradually decrease.
- Reward
- like
- Comment
- Share
From 'Darknet drug lord' to Cryptocurrency entrepreneur, Silk Road 2.0 creator Blake Benthall's decade-long road to redemption

In May 2023, Caduceus on-chainissuanceed the first Memecoin LayerShit. Reading through its Twitter, you can still see traces of its war on capital in the prominent introduction. The label also boldly states: "Developers and projects hijacked by capital are all garbage, including Ethereum and its layer2".

Idealism of Layershit
Questioning and attacking a project larger than oneself is likely to arouse suspicion, especially since Layershit is a memecoin. It is not wise to pick on the Ethereum ecosystem which is thousands of times larger than itself.
However, Layershit doesn't mind the 'praying mantis trying to stop a car' comment. On Twitter, he mentioned, 'We were also developers on Ethereum at first, but since he was hijacked by capital, we knew he was sick and it was time to leave, even though he had become very large. But garbage is still garbage.'
In fact, to the initiators of Layershit, technology is pure and sacred, and cannot tolerate any pollution. In their tweets, they mentioned that "ETH actually had various business logic flaws in the early days of its establishment. In the long-term development, they also realized their own problems. However, the brutal growth of ETH has put it in a dilemma, and it can only patch up the original foundation for business expansion. For the concept of layer2, which aims to solve the scaling problem of ETH, but due to the backlash of capital and traffic competition, excessive Airdrop incentives have become a gathering place for wool parties. The congested layer2 and high gas fees will truly exclude users and developers who have demand for blockchain.

Therefore, as the meme season brews and gas fees rise, Layershit chooses to pour a bucket of cold water because the initiators of Layershit consider that this crazy industry must make some changes.
The main factor that prompted this decision was their aversion and disappointment towards capital. He mentioned that the recent meme frenzy has caused the gas fees on the Ethereum on-chain to skyrocket, which has dropped the users' experience with the blockchain and harmed the interests of on-chain developers. However, even in this situation, users still have expectations for Ethereum and its scalability technology. The manipulation behind all of this is driven by capital, using subsidies, creating trends and public opinion, and turning users' behavior into profit-seeking and speculation. This has resulted in some excellent technologies being unable to be showcased to the public.

"What is a scammer, promises that contradict the facts are scams, and those who claim to solve a certain technical problem but have not solved it are scammers**.**"
Within a few short days, Layershit has released over 90 tweets criticizing half the industry, yet also gained support from many sympathizers. What exactly gives Layershit the confidence to be a 'one-man army'?
The answer is obvious, backed by another team with pure technical ideals, Caduceus, which is the confidence.

Actually, friends who follow the Caduceus public chain can easily perceive that from carrying out developer activities to cooperating with external traffic from various districts, Caduceus has been trying to actively enter the public's field of vision.
"What changes can it bring to the industry?" This is Caduceus Chain and Lyershit's reflection and introspection on the industry as a whole.
Doing the right thing will eventually stay
Those who truly immerse themselves in technology cherish freedom and pursue spontaneous innovation. They do their utmost to open their senses and use code to experience the world, forming a new worldview in the process. As the initiator of Layershit said, "The development of blockchain is a long-term process, not a one-time capital injection."
What does a real blockchain look like? The founder of Layershit, in a simple and straightforward manner, answered, 'Cheap and easy to use.' In his eyes, technology is always very pure, with a hint of adventurous radicalism and romanticism.
In the entire industry, there is no lack of projects that are doing 'persuasion' work. TPS, Consensus, economic system... They use self-created technical descriptions as gimmicks, but often overlook the 'essence'.
The purpose of Layershit seems to have been covered with the filter of 'idealism'. But the initiators of Layershit admit that 'doing the right thing will always stay'.
Afterword
Although I haven't had any contact with them, it is not difficult to see from Layershit's social media that this team is basically a group of people immersed in the world of "technical aesthetics", extremely self-centered and abstract.
"Started with MEME, ended with ideal." This is my evaluation of Layershit. I hope Layershit and its Caduceus blockchain can always adhere to their pure technical ideals and provide a "cheap, easy-to-use" platform for real blockchain developers and users.

Click 'Read the original' to visit the Lyershit official website.
- Reward
- like
- Comment
- Share
Apart from Trump, which other politicians will attend this year's BTC conference?
Author: Shelly, Nianqing, ChainCatcher
Bitcoin Magazine CEO David Bailey today confirmed that Vice President Harris will not speak at the BTC 2024 conference. Despite Harris's absence, this year's BTC conference is not lacking in the presence of American politicians. The conference has invited 10 American political guests, including Trump, of which 8 are Republicans, only one is a Democrat, and one is an independent (former Democrat).

Of course, it is not surprising. On the one hand, the host Nashville in Tennessee is traditionally a 'red state', the stronghold of the Republican Party, and both senators from Tennessee will attend. On the other hand, compared to the conservatism of the Democratic Party, the majority of Republicans hold an optimistic attitude towards Crypto, with a recent survey by Paradigm showing that 28% of Republicans hold or have purchased Cryptocurrency, exceeding the national average, and 60% of Republicans tend to have Congress explicitly regulate encryption. A more intuitive data point is that in May of this year, the Republican-dominated FIT21 bill was passed and promoted. The following figure intuitively reflects the voting results of the two parties and their attitudes towards the regulation of digital assets. Recently, the Republican National Convention also approved a new agenda proposed by Trump for the Republican Party, one of which is to support innovative encryption policies.
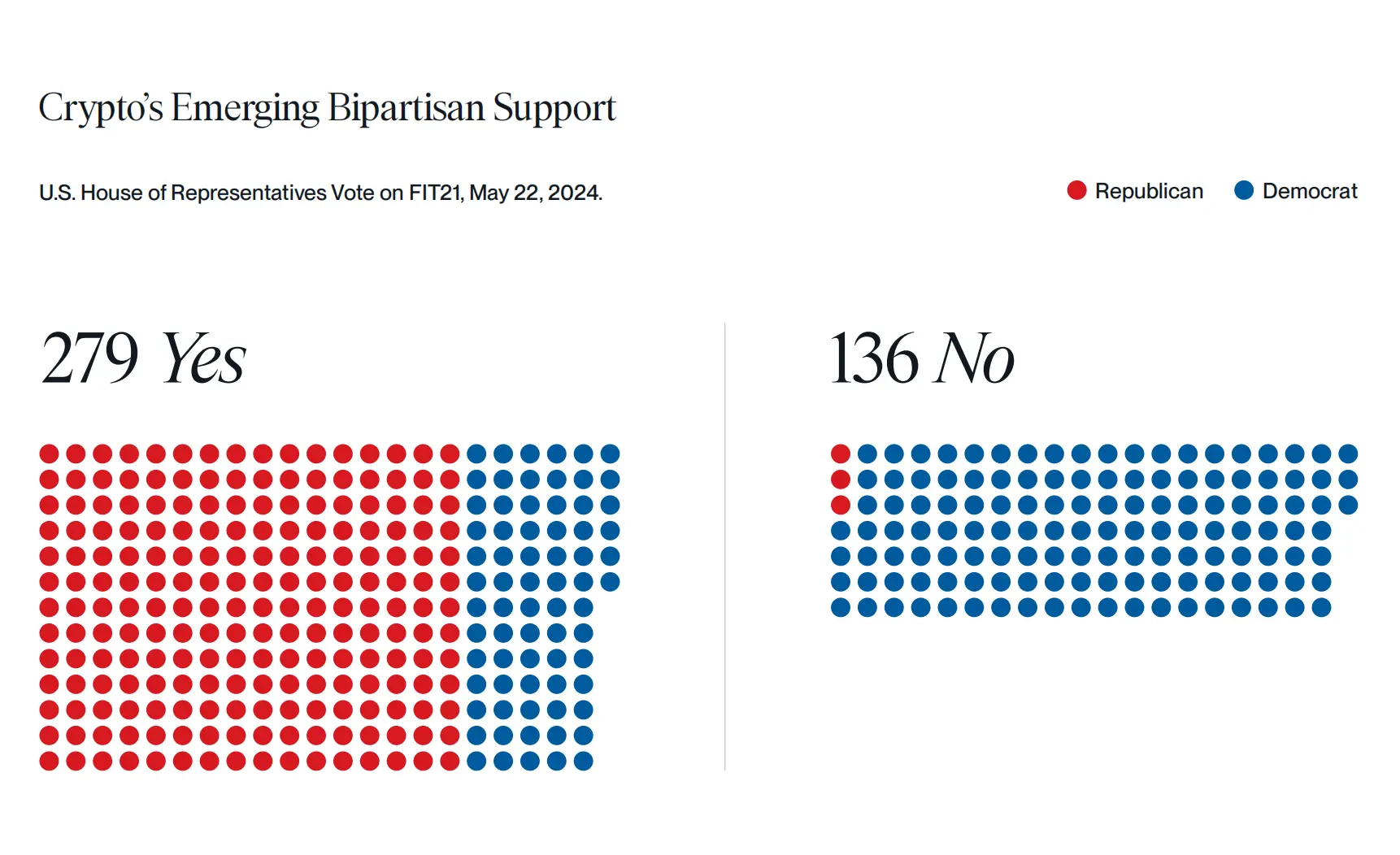
Voting on the FIT21 bill by the two parties, source: Bitwise
Let's go back and talk about the politicians who participated in the BTC conference and their promotion of encryption.
- Donald Trump: 2024 US presidential election candidate, former 45th President of the United States, Republican, self-proclaimed as the "Crypto President", and his involvement in the encryption field can be read in our previous article "Selling Trump: Former President's encryption Business Circle and "Business Book""
- Vivek Ganapathy, a Republican candidate who ran for the 2024 US presidential election, announced during his campaign that he would accept BTC as campaign donations. On January 15, 2024, he announced his withdrawal from the presidential primary.
- Bill Hagerty is a Republican Senator from Tennessee. He criticized the Democratic Party for being too centralized and restrictive in its approach to the encryption industry.
- Marsha Blackburn is a senator from Tennessee, a Republican. She announced in this year's re-election campaign that she accepts Cryptocurrency donations and appreciates the freedom and privacy of BTC.
- Cynthia Lummis is a senator and federal representative from Wyoming, a Republican, a BTC supporter, and has been pushing for BTC-related legislation. She has stated that BTC and cryptocurrency will become an important part of the future economy. She also plans to announce BTC strategic reserve legislation at the BTC conference.
- Tim Scott is a senator from South Carolina, a Republican, and a member of the U.S. Senate's Financial Innovation Core Group. He has repeatedly called for a balanced approach to digital assets and advocated for the development of a Cryptocurrency regulatory framework.
- Bernardo Moreno is a Republican Senate candidate, a Republican, and a blockchain entrepreneur and Cryptocurrency enthusiast.
- Sam Brown is a Republican candidate for the US Senate, a Republican, an early adopter of Cryptocurrency, and invested in BTC in 2017.
- Robert F. Kennedy Jr. is an independent candidate for the President of the United States. He was a Democrat before 2023 and currently belongs to other independent parties. He has purchased 14 BTC and has repeatedly expressed support for blockchain, BTC, and cryptocurrency, such as hoping to allocate the entire U.S. budget on-chain, and promising to release the founder of the Silk Road platform if elected president.
- Ro Khanna is the only Democrat attending the conference, serving as a U.S. congressman since 2017. The progressive Democrat represents a district, including Silicon Valley, which has a friendly attitude towards Cryptocurrency. The highly-followed Cryptocurrency policy roundtable this month was hosted by Ro Khanna, who has been in contact with senior executives in the digital asset industry, Democratic lawmakers, and White House officials.
P.S. Although encryption has become a battleground for voters of both parties and favorable information for the development of the entire industry, in the long run, cooperation between the two parties is needed in order to promote the development and regulation of the encryption industry, which is healthier for the entire ecosystem.
- Reward
- like
- Comment
- Share
- Topic
- Pin
- 🔥 Join "Suggested Topics" Campaign & Win Weekly Points Rewards
How to join:
1.Visit Gate Post APP page
2.Click any top 3 "Suggested Topics"
3.Users who post quality content under "Suggested Topics" will be selected to win rewards.
🎁 Lucky winners will receive $20 Points each
More: https://www.gate.io/article/33633
- 📢Gate.io trading robot community ambassador benefits upgrade!
📝 Easy tasks, happy points winning!
Achieve the required points to receive rewards on a monthly basis!
💰Individuals can receive up to 100 USDT per month!
If you: 👇
Familiar with trading robots and their operation mechanisms.
Frequently active in different communities. Have community management experience.
🚀 Immediately private message the administrator (https://t.me/Gate_CopyTrading) to sign up and win rewards!
- #交易机器人 # Strategy Trading # #TianDiDan # 新人奖励# #BTC # ETH#
🔥 Gate.io Earth Single Special Event Win 10,000 yuan prize!
📈 HoldingsBTC believers cannot miss!
🎁 New users' first order strategy enjoy 1,000 USDT welcome gift!
🏆 Trade and enjoy high bonuses + VIP upgrade vouchers and other rewards!
🔗 Join the registration: https://www.gate.io/zh/announcements/article/38059
- 🫵 We want you, Crypto Observer!
🎉 Become a Gate.io Post Crypto Observer & Win Daily Great Rewards!
🌟 How to join?
1.Share daily crypto news, market trends, and insights into your post.
2.Include the #CryptoObservers# to successfully participate.
🎁 5 lucky "Crypto Observers" will be rewarded $2 token rewards each weekday!
📌 The winners list will be announced daily, and rewards will be distributed together next week.
⏰ Ends at 16:00 July 31 UTC
- 🎁Attention! A Gate.io grand prize is waiting for you!
➡️ Vote for your favorite content creators and streamers!
🎁 Win a MacBook Air and exclusive merch!
📅 Jul 8 - Aug 4 (UTC)
🗳️Vote Now: https://gate.io/activities/community-gala
More: https://gate.io/announcements/article/37717
- About
- Products




